Apparently Transport for London are dealing with a cyber security incident.
-
dangercakereplied to Ryan Castellucci :nonbinary_flag: on last edited by
@ryanc @GossiTheDog _"vendor did a fucky wucky"_ is beautiful, and from today I'll be looking for ways to use it in documentation
 https://attack.mitre.org/techniques/T1199/
https://attack.mitre.org/techniques/T1199/ -
Ryan Castellucci :nonbinary_flag:replied to dangercake on last edited by [email protected]
@dangercake @GossiTheDog TBH, I originally wrote "hardware" instead of "vendor", but "vendor" includes hardware failures, us-east-1, and whatever nonsense clownstrike is up to.
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Transport for London have shut down outbound internet access and restricted systems inbound, eg they have cut off some Netscaler VPNs but left up others for home users.
They appear to be doing a containment. Unclear if ransomware so far as haven’t had time to crawl network traffic.. but it’s the containment steps you take for ransomware and extortion groups.
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Looked into this, the TfL API server for tube data is down (has been for about a day)
JF :debian: :verbike: (@[email protected])
@[email protected] Citymapper is showing a message saying that due to the cyber incidents, live tube timetable is not available. Strangely enough, the bus timetable also provided by TFL are still available

Rouge.eu.org (rouge.eu.org)
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
The Transport for London cyber incident is still ongoing.
The attackers got onto the corporate network, which is currently contained for recovery.
The operational (ICS) network wasn’t reached so services to customers continue uninterrupted.
Boundary internet services often offline, VPN restricted to home users, ERP systems, API systems etc offline.
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
If anybody is interested, the Transport for London cyber incident is still ongoing 3 days later - systems remain contained.
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Two of the systems shut down
 https://beta.shodan.io/host/195.40.85.10
https://beta.shodan.io/host/195.40.85.10 -
Kevin Beaumontreplied to Kevin Beaumont on last edited by
If anybody is wondering, Transport for London are still in containment 5 days in.
APIs, ERP etc still offline.
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Update on Transport for London incident.
I can see prior traffic from their network to a crimeware group. #tfl #threatintel
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Transport for London are still in containment phase, 7 days into their cyber incident.
Hopefully it focuses minds on boards who believe large scale cyber incidents can be resolved in a day. #tfl #threatintel
-
Kevin Beaumontreplied to Kevin Beaumont on last edited by
Day 9 of the Transport for London cyber incident
Two updates
- I’ve confirmed they’re still in containment phase, and internal services and API remain down.
- @zackwhittaker has an excellent spot - they’ve removed the statement about no evidence of customer data exfiltration, and then not commented when asked about it. https://techcrunch.com/2024/09/10/londons-transit-agency-drops-claim-it-has-no-evidence-of-customer-data-theft-after-hack/
-
Kevin Beaumontreplied to Kevin Beaumont last edited by
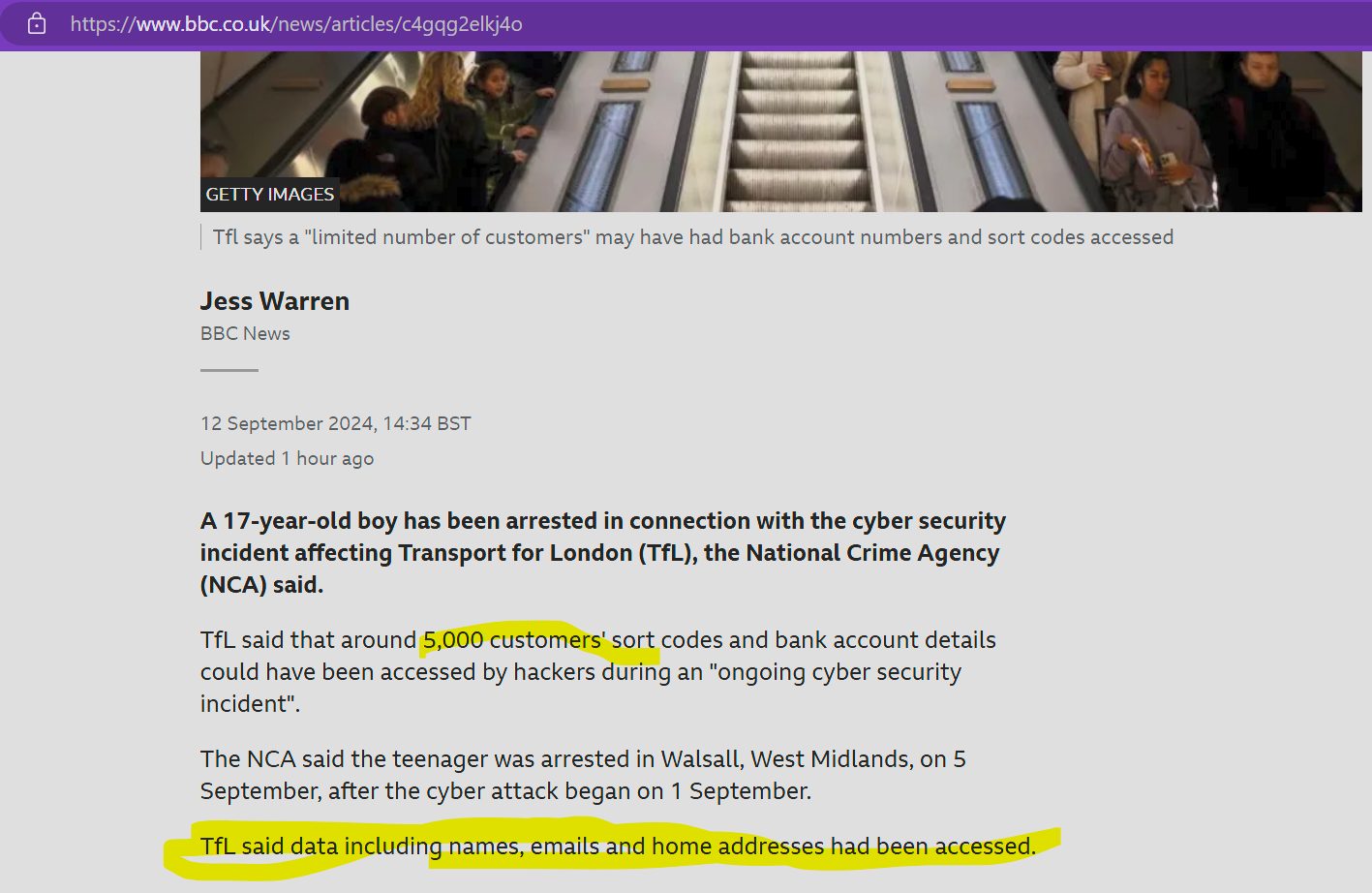
Transport for London tell me they have identified data exfiltration of customer names, contact details, email addresses, and - in a small number of cases - bank account numbers and sort codes.
They are still in containment phase. #tfl #threatintel
-
Kevin Beaumontreplied to Kevin Beaumont last edited by
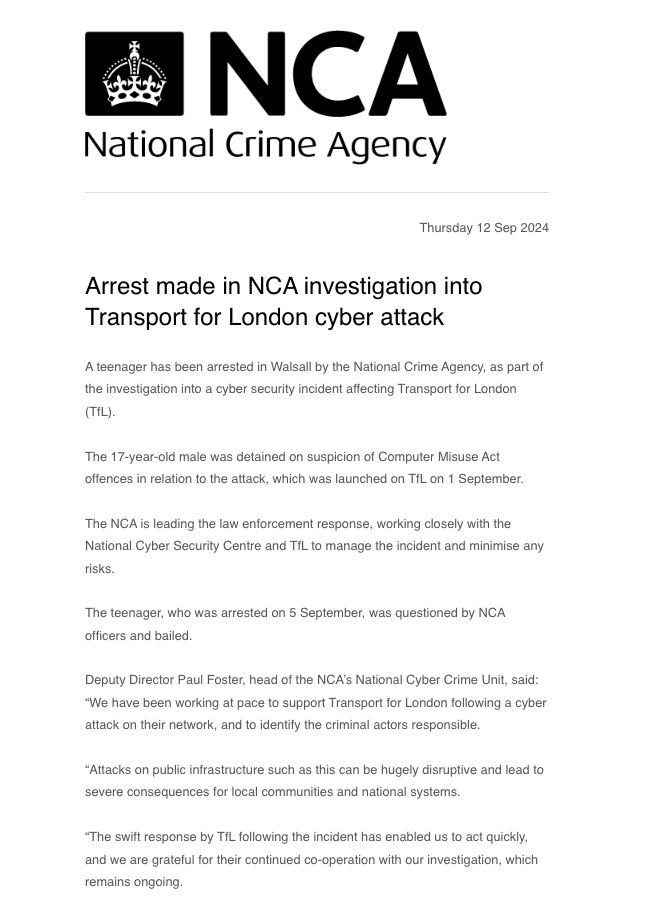
The NCA have arrested a teenager over the Transport for London hack HT @mattburgess #tfl #threatintel
-
Kevin Beaumontreplied to Kevin Beaumont last edited by
For any press covering the #TfL hack - the 5000 bank accounts is separate to the customer names, emails and home addresses bit.
TfL didn't say how many people's details overall were accessed.
-
Kevin Beaumontreplied to Kevin Beaumont last edited by
One of the things TfL have done in their containment phase is locked their IT staff's accounts, who aren't working on recovery -- and they're working to manually reauthenticate who their staff are, i.e. check their identities.
In entirely unrelated (
 ) news, teenagers in LAPSUS$ and Scattered Spider often obtain access by calling up the helpdesk and saying they've lost their phone for MFA and/or forgot their password. Your containment playbooks should include stripping MFA devices.
) news, teenagers in LAPSUS$ and Scattered Spider often obtain access by calling up the helpdesk and saying they've lost their phone for MFA and/or forgot their password. Your containment playbooks should include stripping MFA devices. -
Kevin Beaumontreplied to Kevin Beaumont last edited by
Transport for London latest - they are resetting the login and MFA details for 30,000 employees in person, accounts are locked. #TfL #threatintel
-
Kevin Beaumontreplied to Kevin Beaumont last edited by
The #TfL queue to get account access back is out the buildings and down the roads #threatintel