Is there a cloud "throw money at the problem" service that cracks md5crypt passwords with GPUs?
-
Richard "mtfnpy" Harmanreplied to Royce Williams last edited by
@tychotithonus dunno what is in the /yealink/config filesystem yet. Haven't found a way into the device yet. I *did* manage to figure out how to enable telnet, through config it fetches via provisioning.
-
legnadibromreplied to Richard "mtfnpy" Harman last edited by
@xabean @tychotithonus fwiw the Intelbras TIP 200 series shares the same shadow entries; dead end finding any working creds attributed though
CVE-2020-13886/README.md at master · Ls4ss/CVE-2020-13886
Exploit CVE-2020-13886 - LFI Intelbras TIP 200 / 200 LITE / - CVE-2020-13886/README.md at master · Ls4ss/CVE-2020-13886
GitHub (github.com)
-
@xabean @tychotithonus running jtr against it and rockyou2024 right now for yucks
-
Richard "mtfnpy" Harmanreplied to legnadibrom last edited by
@morb @tychotithonus mmm whelp I bumped up the logging level through config, and I see when I try to telnet in with root/toor/admin/yealink any username all results in:
login[480]: invalid password for 'UNKNOWN' on 'pts/0'
-
legnadibromreplied to Richard "mtfnpy" Harman last edited by
@xabean @tychotithonus have you tried shell injection in any of the provisioning file fields yet
-
extracted latest fw for TIP200 (60.61.75.22) and...
[Yealink Busybox Ver 1.0.0.1]
BusyBox v1.10.3 (2013-08-06 13:53:41 CST) multi-call binary
Copyright (C) 1998-2007 Erik Andersen, Rob Landley, Denys Vlasenko>_<
-
Richard "mtfnpy" Harmanreplied to legnadibrom last edited by
@morb @tychotithonus my head was in the same place - the "diagnosis" page that apparently had straight up shell injection isn't in the firmware I'm running on this phone, and now I'm digging into some of the MACADDRESS.cfg provisioning files and related XML translation on the phone checking what gets (ab)used by grep into shell variables, etc.
-
Richard "mtfnpy" Harmanreplied to Richard "mtfnpy" Harman last edited by
@morb Oh neat, does this URL work on your phone?
/servlet?p=hidden -
legnadibromreplied to Richard "mtfnpy" Harman last edited by
@xabean don't have one on hand; just the latest firmware I could find for a rebranded Yealink that had the same shadow file -- will dig for that tho
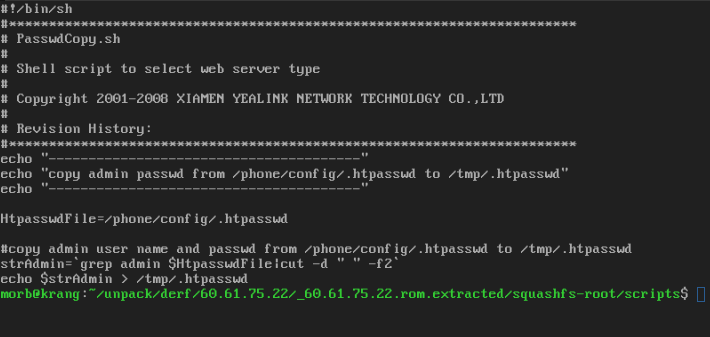
PasswdCopy.sh looks like it uses an unsafe subshell fwiw
-
Richard "mtfnpy" Harmanreplied to legnadibrom last edited by
always fun when running strings on a piece of firmware and you find:
user:s7C9Cx.rLsWFA
var:jhl3iZAe./qXM
admin:uoCbM.VEiKQto -
Ryan Castellucci :nonbinary_flag:replied to Richard "mtfnpy" Harman last edited by
