One thing that fascinates me about this private computing is that every big cloud vendor has similar sounding efforts but they never quite come together into a useful package - like baking cookies without the flour.
-
One thing that fascinates me about this private computing is that every big cloud vendor has similar sounding efforts but they never quite come together into a useful package - like baking cookies without the flour.
Lots of hopes and dream, but lacking guidance and a concrete go-to-market roll out plan.
To this day, most advanced secure computing hardware sits unused because we don’t surface the primitives in any actionable form. https://infosec.exchange/@mattburgess/113124728485246481
-
Dave Winer ☕️replied to Miguel de Icaza ᯅ🍉 last edited by
@Migueldeicaza -- not sure specifically what you're thinking of but we never finished implementing the web as a virtual computer. identity and storage have to be intimately connected. but the companies that could do it, and it has to be done by companies, don't make the connection. amazon imho should rule here.
-
Miguel de Icaza ᯅ🍉replied to Dave Winer ☕️ last edited by
@davew stuff like this: https://azure.microsoft.com/en-us/solutions/confidential-compute
-
Kingsley Uyi Idehenreplied to Miguel de Icaza ᯅ🍉 last edited by
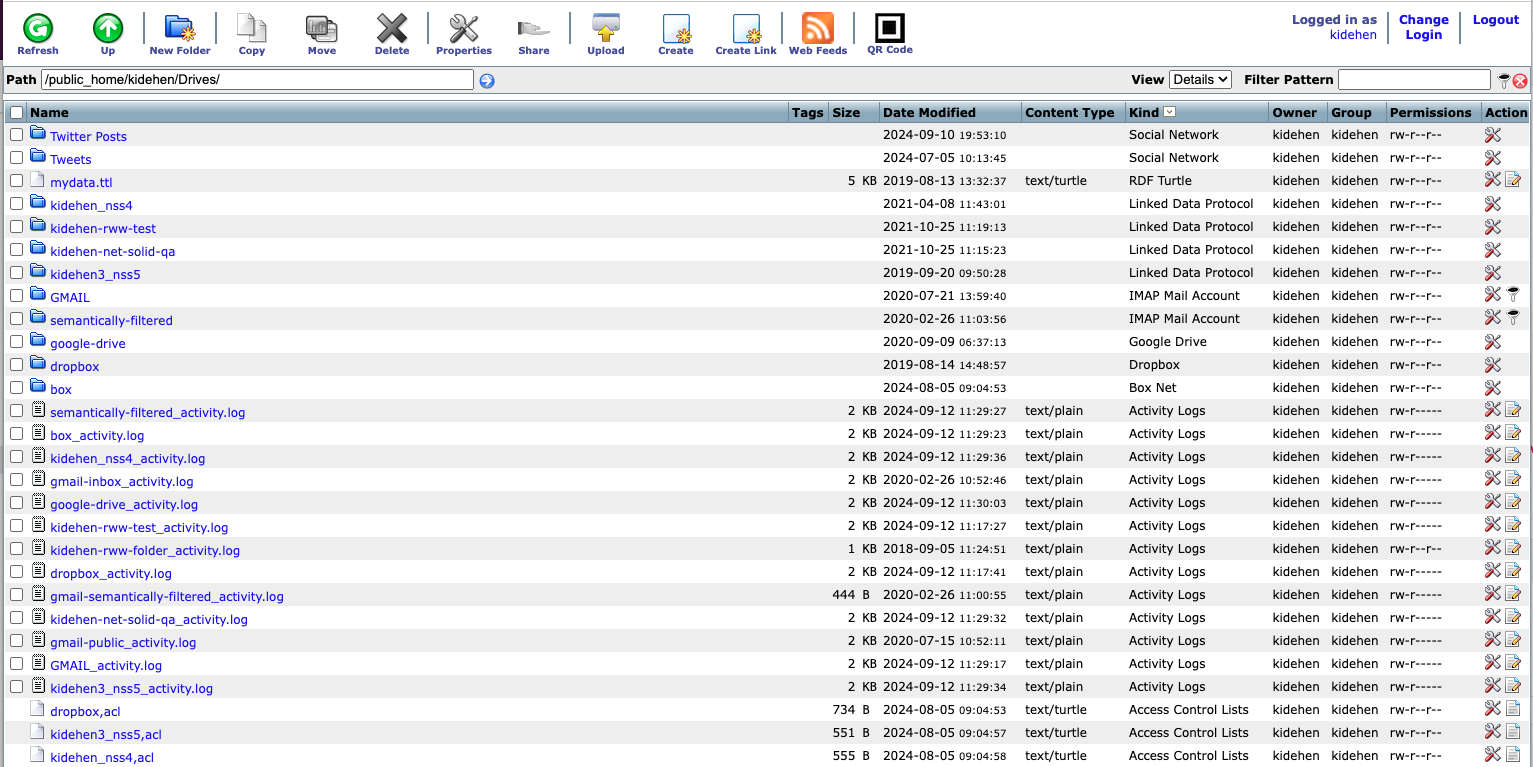
For years, we’ve offered a personal #DataSpaces platform providing an abstraction layer over data managed by #filesystems (including cloud services) and/or #DBMS.
You can even mount #Dropbox, #OneDrive, #S3, etc., with fine-grained access controls for governance.
In the age of #AI, we’re making this usable via natural language as an extension (e.g., #CustomGPT) for #LLM-based chatbots like #ChatGPT.
-
Kingsley Uyi Idehenreplied to Kingsley Uyi Idehen last edited by
Long story short, Dropbox, Box, OneDrive, Google Drive, etc., all dropped support for “Public” folders. Our abstraction doesn’t. It allows operators of #ODSBriefcase “mounted folders” to set fine-grained, attribute-based access controls scoped to folders or specific files. It also handles #identity, loosely coupled with authentication protocols. In fact, you can even use sophisticated queries to define these access controls.
