yes i need to rewrite my personal statement, no i don’t know how to talk about myself,
Posts
-
apparently i’ve cracked $10/week on https://liberapay.com/trwnh — can we get to $20? :bongoCat: -
apparently i’ve cracked $10/week on https://liberapay.com/trwnh — can we get to $20? :bongoCat:apparently i’ve cracked $10/week on https://liberapay.com/trwnh — can we get to $20? :bongoCat:
-
oh god they made twitter dark by default for logged out users now. its so joever@codl really? that’s weird, it’s not visible at all for me
-
in a way posting source code online is like posting nudes@Dee no, posting source code is like posting dna. if you want the equivalent of nudes, that’s an unstyled frontend. engineering blog posts are the equivalent of x-rays,
-
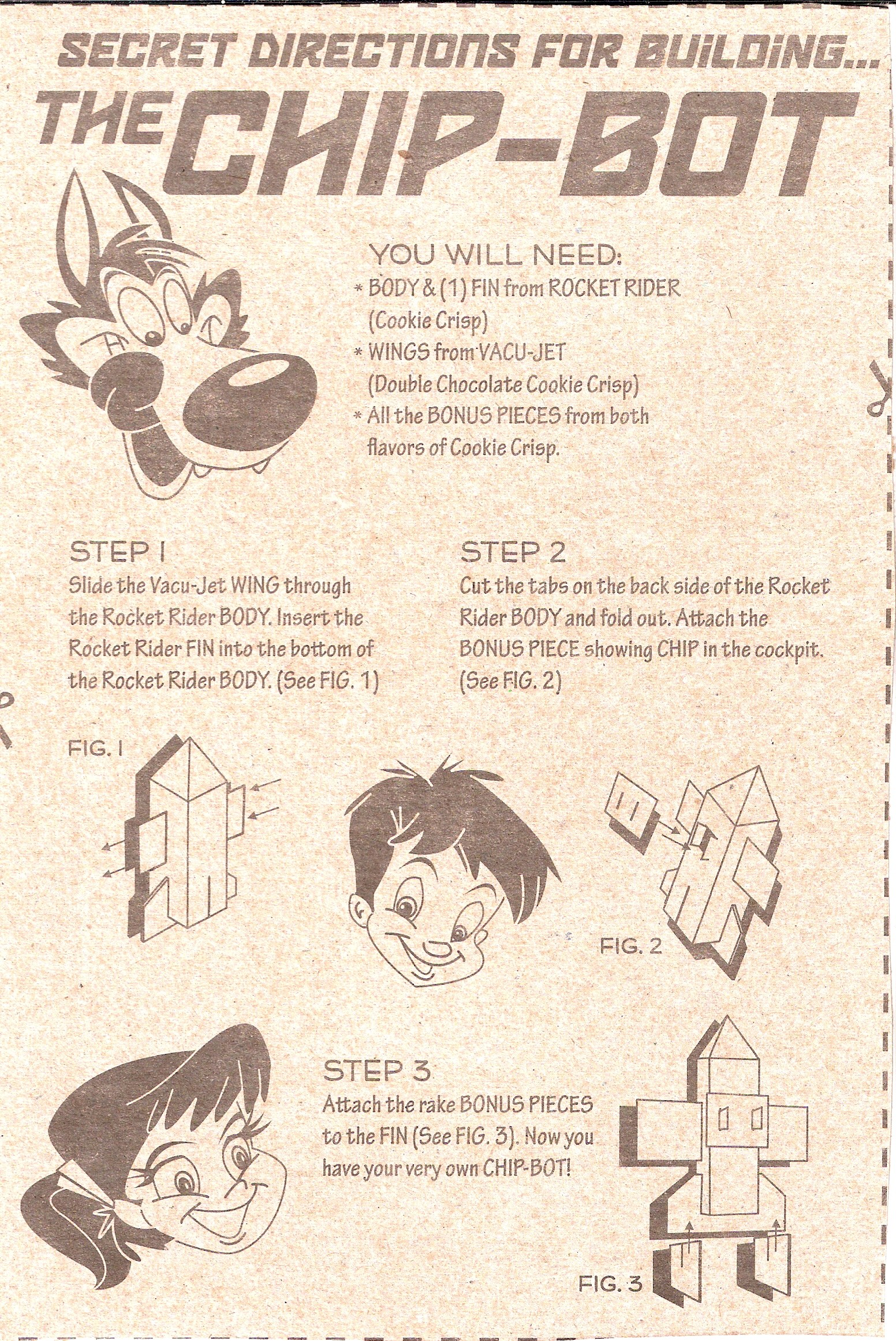
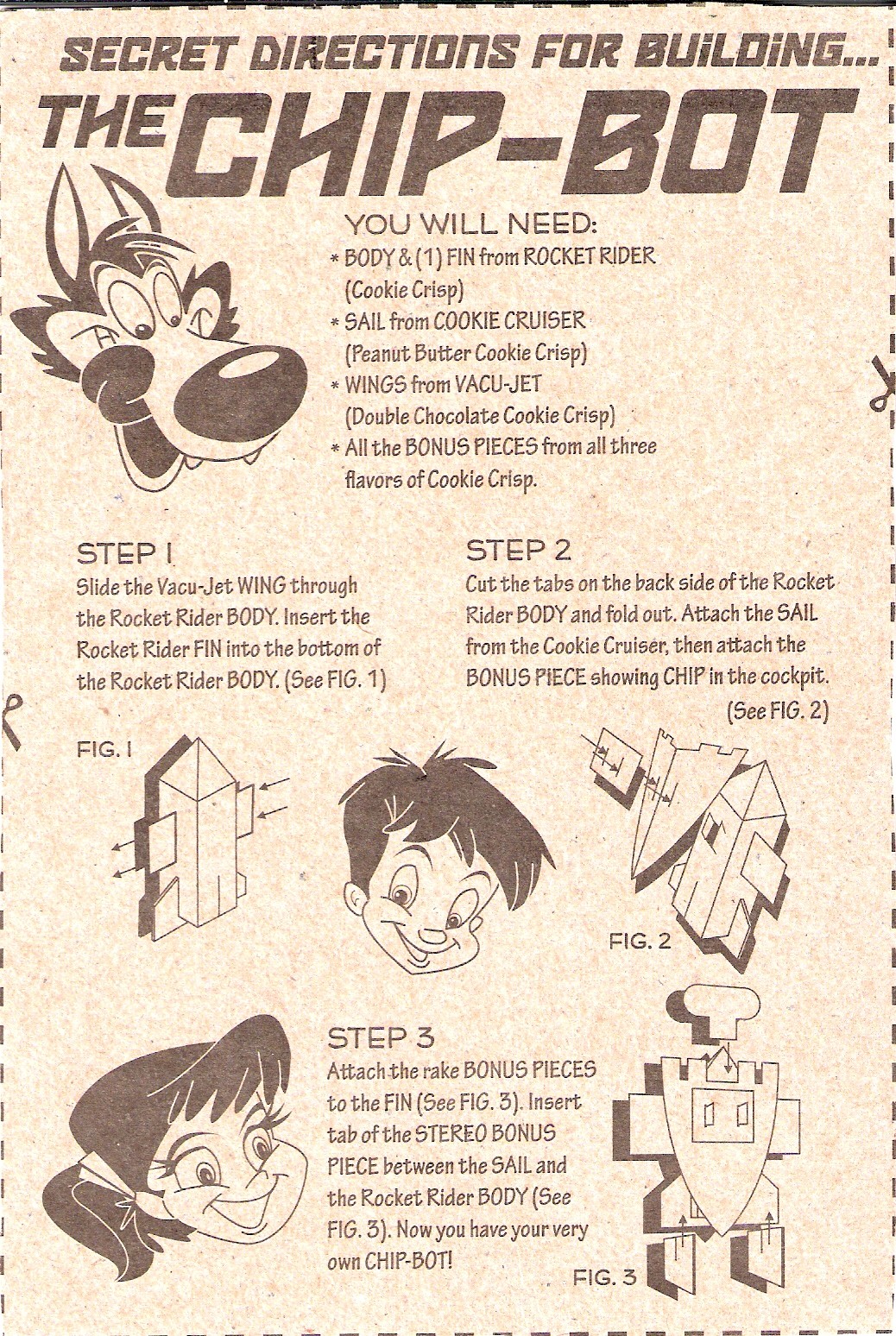
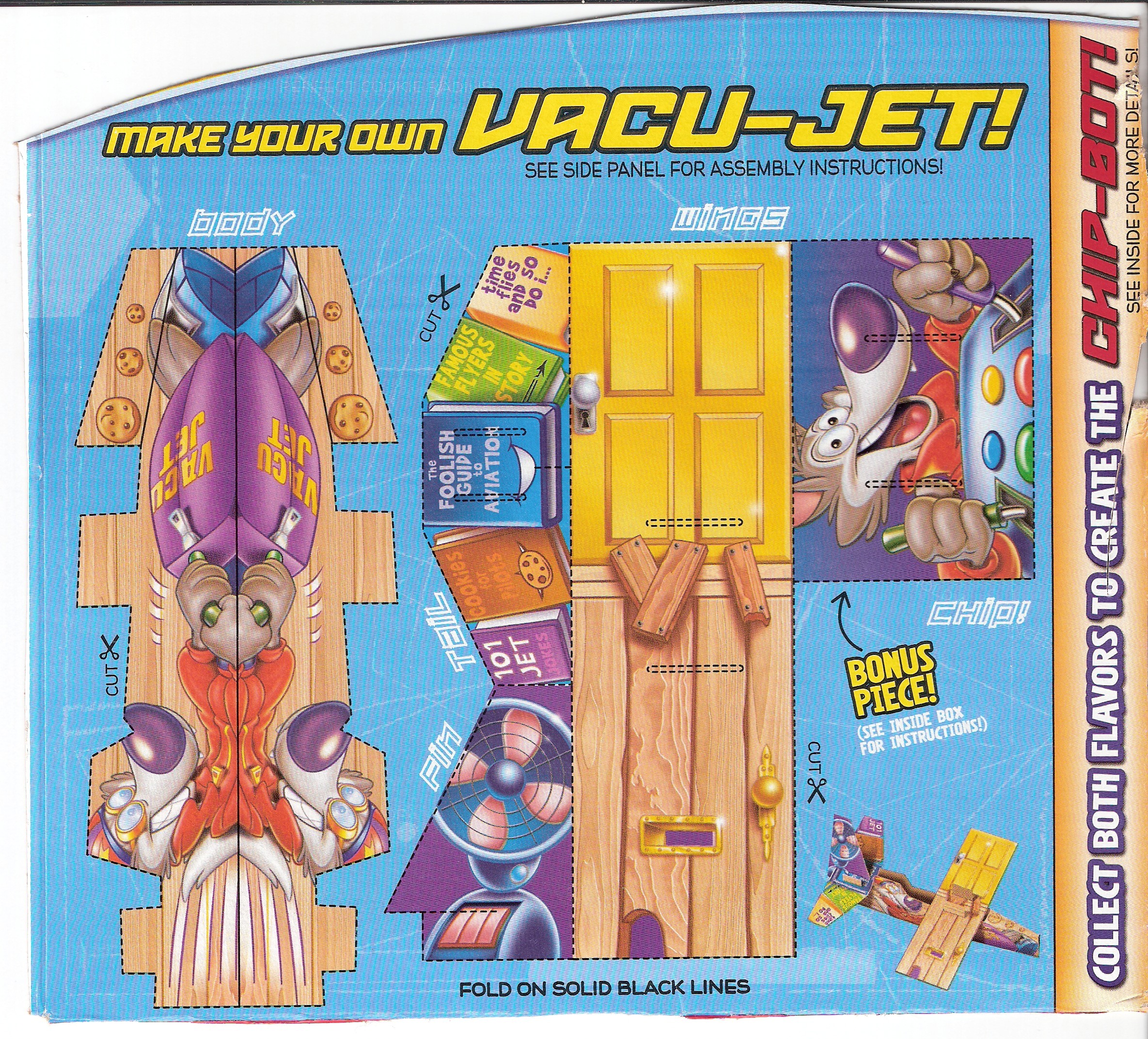
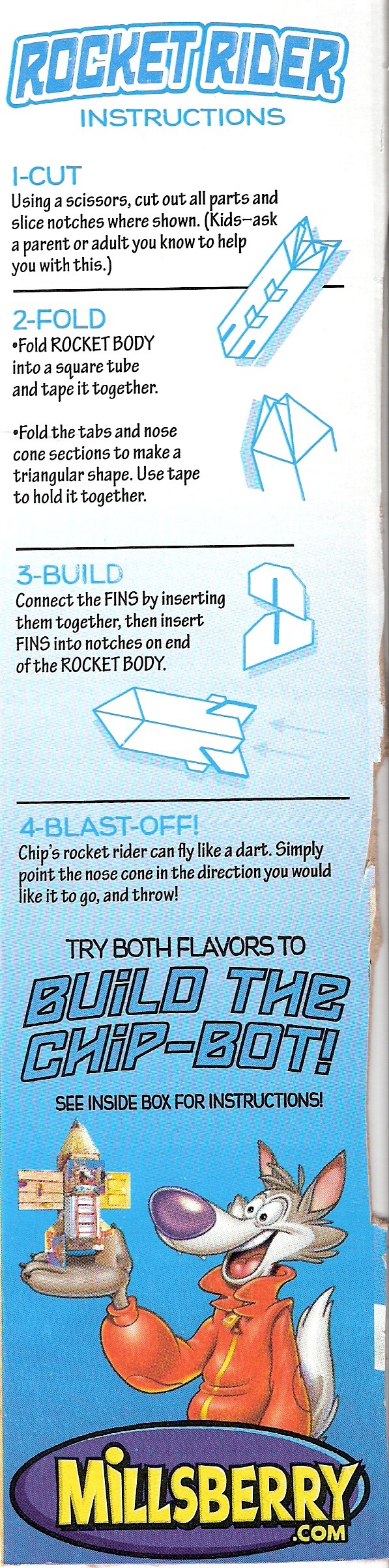
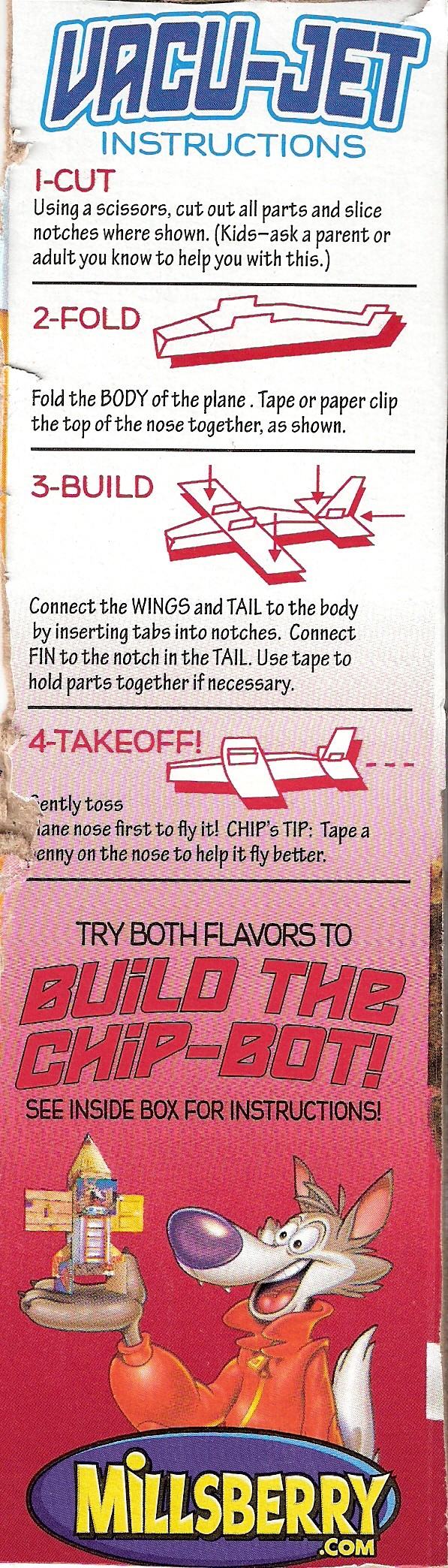
i may be the only person who has these pictures on the internet, or possibly ever, thanks to me c. 2008 #CookieCrisp #papercraftanyway if you ever need to know what kinda person i am, i'm the type of person to not only scan papercraft from cereal boxes and lunchables snacks, but also to keep the files around for years to come
-
@noiob smh gimme the chance to type out all the alt text, i was working on it@noiob smh gimme the chance to type out all the alt text, i was working on it
-
i may be the only person who has these pictures on the internet, or possibly ever, thanks to me c. 2008 #CookieCrisp #papercraftsadly i am haunted by the knowledge that they later updated the #ChipBot to require 3 flavors of cereal instead of 2. I never bought the 3rd flavor. #CookieCrisp #papercraft
-
i may be the only person who has these pictures on the internet, or possibly ever, thanks to me c. 2008 #CookieCrisp #papercrafti may be the only person who has these pictures on the internet, or possibly ever, thanks to me c. 2008 #CookieCrisp #papercraft

-
it would be cool if there was a way to do the equivalent of an http HEAD request, but for html documents@CobaltVelvet i'm wondering if there's a way to get nginx or whatever to parse the head element of an html file and inject http headers corresponding to them somehow
-
it would be cool if there was a way to do the equivalent of an http HEAD request, but for html documentsit would be cool if there was a way to do the equivalent of an http HEAD request, but for html documents
-
https://datatracker.ietf.org/doc/rfc7239/@erincandescent also the problem with fetching posts today is a lack of standardization of cross-domain authentication/authorization. you can do Authorization: Bearer or Authorization: Signature (with the finalized version of http message sigs) or you can authenticate directly at the remote site with IndieAuth or OIDC or OpenWebAuth or whatever. The hard part is picking one that everyone should support
-
https://datatracker.ietf.org/doc/rfc7239/@erincandescent not necessarily, it’s a bigger problem with inbox forwarding because you don’t actually know the recipients, you just know the collection id. and we’re trying to preserve the “single delivery” aspect of activitypub so that you *don’t* have to fetch anything
-
https://datatracker.ietf.org/doc/rfc7239/@erincandescent how do you know the actor is authorized
-
https://datatracker.ietf.org/doc/rfc7239/@erincandescent what if it’s private
-
Hmm... Terrible Comment.Hmm... Terrible Comment.
-
https://datatracker.ietf.org/doc/rfc7239/@tedu worst case scenario, we verify two http sigs, but in return we do away with ld sigs entirely.
-
https://datatracker.ietf.org/doc/rfc7239/@tedu i think that wont work for private messages
the initial conceit was, we could still get rid of ld sigs and even keep replay prevention by forwarding the original signature using the Forwarded: header. this requires storing no additional info, just verifying the forwarded signature (and verifying the same-origin policy, which is the real underpinning here). this assumes we don't care to authenticate the forwarder... which we might care, for example to prevent spam forwards.
-
https://datatracker.ietf.org/doc/rfc7239/@tedu i guess that's true for objects but not really for activities. if you signed only the digest for activities, then you could intercept and record a Create activity and replay it even after they send out a Delete. the next counterstep would be to include/require a timestamp within every activity, i guess. which... it's probably "enough" to include the timestamp anywhere, really? in the activity, in the http request, in the ld sig, whatever.
-
https://datatracker.ietf.org/doc/rfc7239/@tedu we're basically saying that for POST requests, not only do you need to verify that the content was unmodified, but also you want the signature to only apply to the POST /inbox request made at a certain Date to a certain Host. this prevents replay.
-
https://datatracker.ietf.org/doc/rfc7239/@tedu like, if you signed only the digest then would that be "enough"? these kinds of security decisions aren't really documented anywhere
