FYI: Red Hat blog post on the CUPS vulnerability at https://www.redhat.com/en/blog/red-hat-response-openprinting-cups-vulnerabilities Security Bulletin at https://access.redhat.com/security/vulnerabilities/RHSB-2024-002?extIdCarryOver=true&sc_cid=701f2...
-
Jan Wildeboer 😷:krulorange:replied to Jan Wildeboer 😷:krulorange: last edited by
@GossiTheDog @dangoodin And big thanks to Till Kamppeter from the Open Printing project who has been working hard to get the fixes in upstream. A true hero since many, many years, IMHO.
-
Jan Schaumannreplied to Jan Wildeboer 😷:krulorange: last edited by
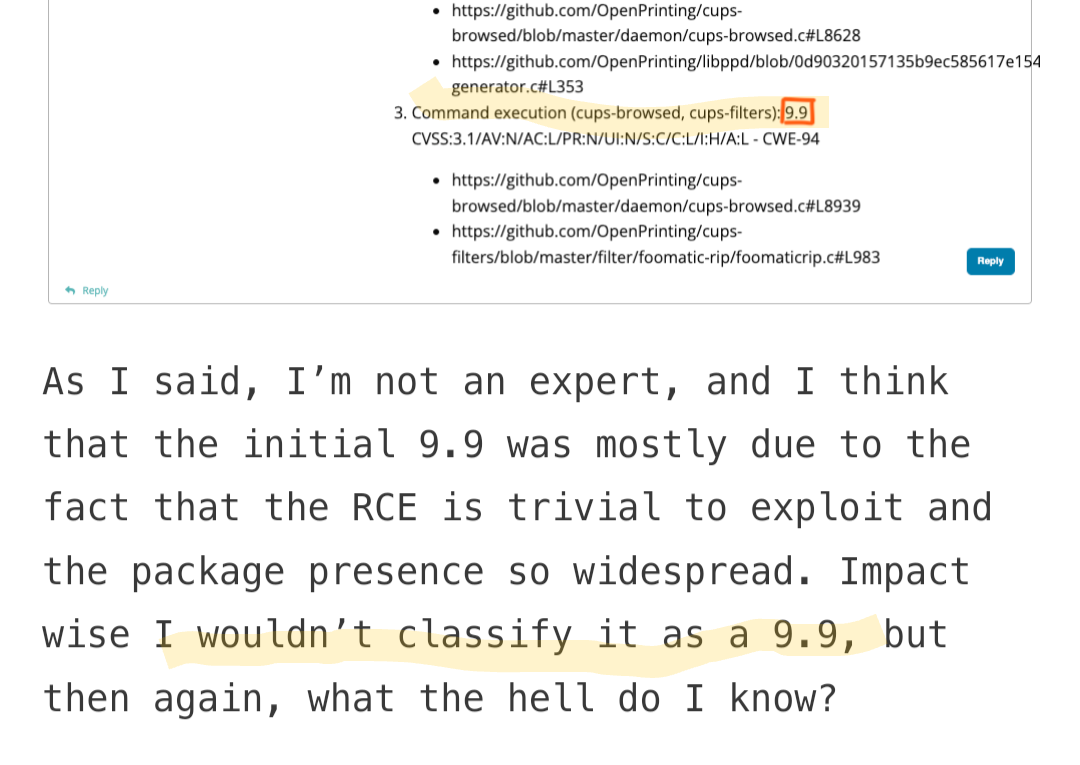
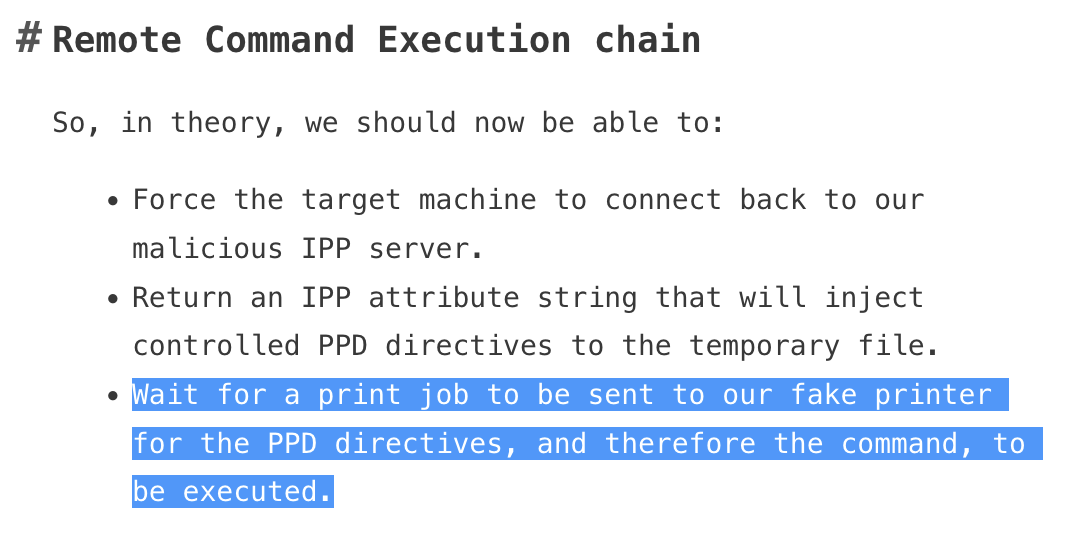
@jwildeboer And I still think that “wait for a user to print something to the malicious printer” counts as “user interaction”, which many scores don’t seem to reflect.
Jan Schaumann (@[email protected])
Attached: 1 image Might be worth calling out that this #cups #rce is dependent on the user sending a print job to the injected/manipulated printer. In my book, that counts as "user interaction", and would yield a CVSS score of CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:H/A:L => 8.8

Mastodon 🐘 (mstdn.social)
-
Jan Wildeboer 😷:krulorange:replied to Jan Schaumann last edited by [email protected]
@jschauma We set UI:N as once the malicious printer shows up, it could also be fed a print job by an automated queue, AFAICS. But I will ask internally about that. UPDATE for CVE-2024-47177 we did set UI:R but that one got a total of 6.2 Full string is CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:L/I:H/A:L see https://access.redhat.com/security/cve/CVE-2024-47177
-
Jan Schaumannreplied to Jan Wildeboer 😷:krulorange: last edited by
Waiting for an automated job still feels like waiting for a cron job to click a link, though, unless the attacker can trigger/inject the job.
¯\_(ツ)_/¯
-
Jan Wildeboer 😷:krulorange:replied to Jan Schaumann last edited by
@jschauma Yep, full ACK. But weird stuff tends to happen at the worst time, so better safe than sorry

-
Peterreplied to Jan Wildeboer 😷:krulorange: last edited by
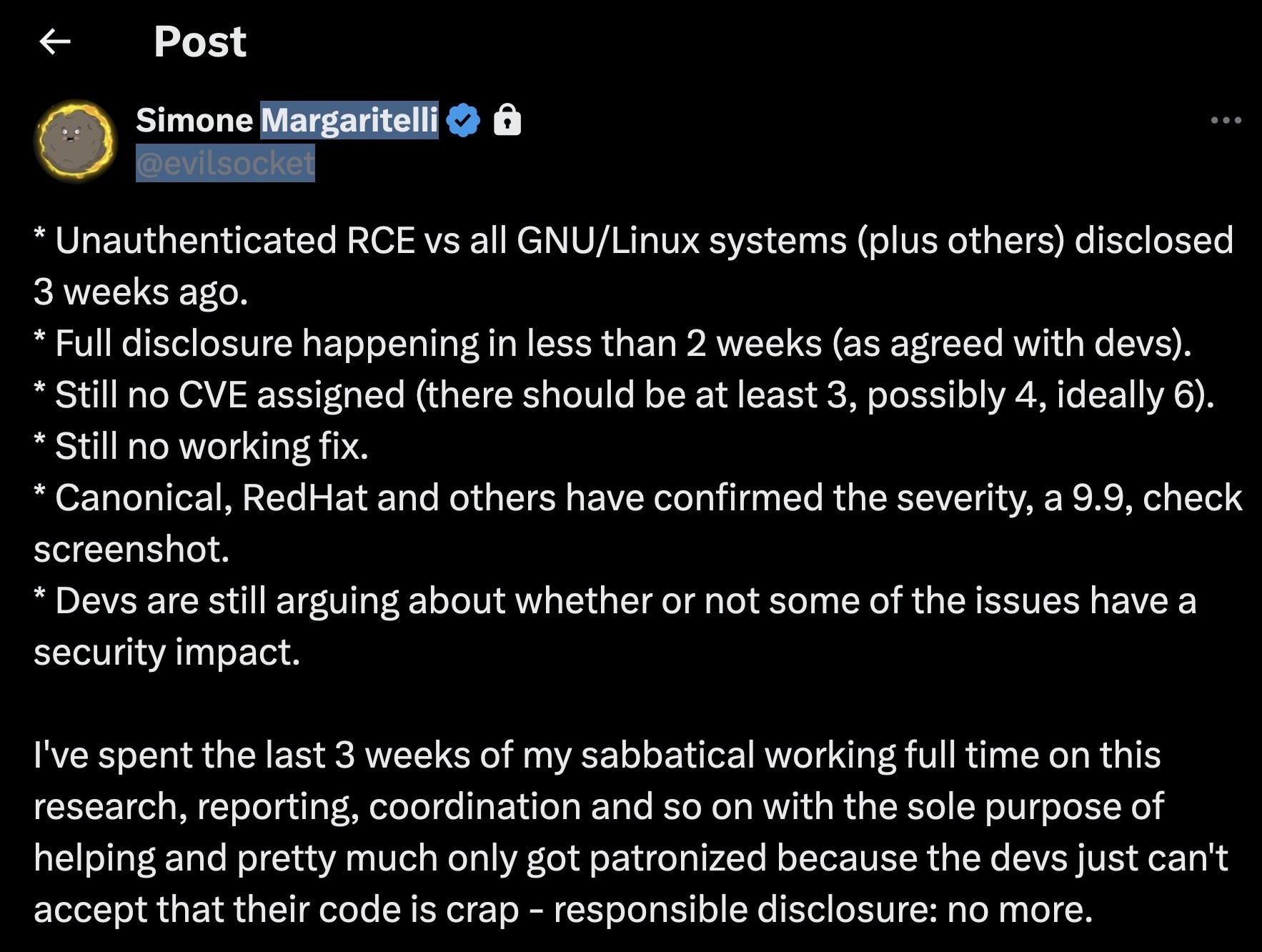
@jwildeboer @GossiTheDog @dangoodin just to confithr original reporter also didn’t say it was a 9.9. He just repeated what he was told. https://x.com/evilsocket/status/1839446031165190523
-
Jan Wildeboer 😷:krulorange:replied to Peter last edited by [email protected]
@plambrechtsen @GossiTheDog @dangoodin in his original Twitter thread he posted a screenshot of internal communication with someone at Red Hat in which the 9.9 was mentioned as *prelaminary* and he presented it as fact, IMHO. He deleted that tweet, it seems. Telling.
-
👾 Rene Rehmereplied to Jan Wildeboer 😷:krulorange: last edited by
@jwildeboer @GossiTheDog @dangoodin quote: "I wouldn’t classify it as a 9.9"
-
Jan Wildeboer 😷:krulorange:replied to 👾 Rene Rehme last edited by
@renereh1 Yep. That kind of behaviour is called backtracking
 @GossiTheDog @dangoodin
@GossiTheDog @dangoodin -
👾 Rene Rehmereplied to Jan Wildeboer 😷:krulorange: last edited by
@jwildeboer @GossiTheDog @dangoodin Maybe I just didn't understand it. In other words, he is referring to an initial CVSS base score that does not apply to his finding, but he claims it is confirmed?
-
Jan Wildeboer 😷:krulorange:replied to 👾 Rene Rehme last edited by [email protected]
@renereh1 He first claimed that Red Hat and Canonical had "confirmed" a 9.9 CVSS, which turned out to be (as he should have known) the preliminary assessment by an engineer, not the final rating. After this was pointed out (and the final scores were made publicly available), he changed his tune, claiming that he never thought it would be a 9.9 and that he really doesn't know how the rating process works anyway in his blog post. @GossiTheDog @dangoodin
-
👾 Rene Rehmereplied to Jan Wildeboer 😷:krulorange: last edited by
@jwildeboer @GossiTheDog @dangoodin Ah ok, I see. Yes well, when he posted that, he just took the communicated value. I can understand that somewhere, regardless of how inflated the announcement was.
-
Jan Wildeboer 😷:krulorange:replied to 👾 Rene Rehme last edited by
@renereh1 And we now know what the scale of this vulnerability is (not really earth-shattering), fixes are being made available upstream and by Linux distributions, a mitigation is available (don't run cups-browsed) so at least I am moving on to new dramas
 @GossiTheDog @dangoodin
@GossiTheDog @dangoodin